2026-05-07: CVE-2026-31431 ("Copy Fail")
Summary
Risk Assessment "Online Systems" (connected to the internet): HIGH
Risk Assessment "Offline Systems" (not connected to the internet): LOW
Affected Systems:
- HOME (UBUNTU 22.04, 20.04) : mitigation procedure below
- HOME APPS (UBUNTU 22.04) : mitigation procedure below
- NODESYS (YOCTO KIRKSTONE) : information will be provided
Mitigation Summary
Systems at high risk (HOME Servers, etc) to be immediately patched
Systems at low risk to be patched as soon as practical
Useful Information about Vulnerability
- https://copy.fail/
- https://ubuntu.com/security/CVE-2026-31431
- https://www.cve.org/CVERecord?id=CVE-2026-31431
- https://ubuntu.com/blog/copy-fail-vulnerability-fixes-available
Measures for Ubuntu Systems (HOME, HOME Apps)
Check if your system is affected
On page https://copy.fail/ you'll find a link to a python script to check whether a system is affected by the vulnerability or not. The file is accessible via https://github.com/theori-io/copy-fail-CVE-2026-31431/blob/main/copy_fail_exp.py
Use responsibly
Run only on systems you own or have written authorization to test. The script edits the page cache of a setuid binary; the change is not persistent across reboot, but the resulting root shell is real. Don't run it on production.
Step 1
Check what is the versions set and Python package running in your system:
Scenario-1:
- Ubuntu 20.04.5 LTS
- Python 3.8.10
Scenario-2:
- Ubuntu 22.04.5 LTS
- Python 3.10.12
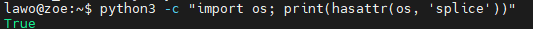
Additionally the script requires an option called OS Splice on Python. The output of the command below must be True:
python3 -c "import os; print(hasattr(os, 'splice'))"Example:
Step 2
If your system is part of Scenario-1 continue with the test below:
grep -qE '^algif_aead ' /proc/modules && echo "Affected module is loaded" || echo "Affected module is NOT loaded"If the result is:
Affected module is loadedcontinue with the mitigation process explained in abstract Mitigating the Vulnerability (Step 6)
In case your system is running on Scenario-2, proceed with the file transfer below, then follow Step 3 to Step 5.
- Transfer the https://github.com/theori-io/copy-fail-CVE-2026-31431/blob/main/copy_fail_exp.py to a directory of your server.
Step 3
Make executable:
chmod +x copy_fail_exp.pyStep 4
Run the script
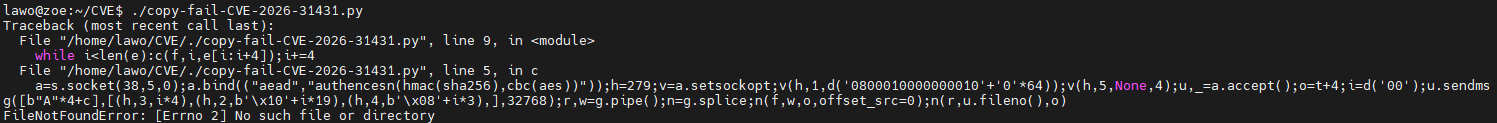
./copy_fail_exp.pyIn case you get this error:
error /usr/bin/env: ‘python3\r’: No such file or directoryYou can fix it by using the command below:
sed -i 's/\r$//' copy_fail_exp.pyStep 5
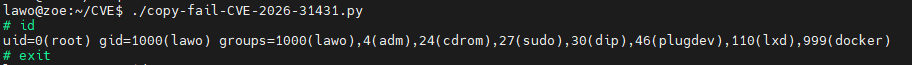
Check the output of the command. The output below shows that the system is affected by the CVE, as the current user has obtained root privileges (uid=0) even though they still belong to gid=1000 (lawo).
Mitigating the Vulnerability
We follow the manual mitigation procedure described on this page: https://ubuntu.com/blog/copy-fail-vulnerability-fixes-available
Step 6
Block the module by creating a /etc/modprobe.d/manual-disable-algif_aead.conf file
echo "install algif_aead /bin/false" | sudo tee /etc/modprobe.d/manual-disable-algif_aead.confStep 7
Reboot the system
sudo rebootConfirming Removal of Vulnerability
In order to validate if the mitigation has been successful, please re-perform Step 4 as described above.
The output of the script run should be similar to the result shown below (script terminates with error):